Cybersecurity Risks in Procurement Software
Procurement platforms handle sensitive supplier, contract, and payment data and connect with core enterprise systems, creating a broad attack surface. Embedding security-by-design into intake, sourcing, contracting, and payables reduces exposure without slowing the business. Zycus brings governance, risk signals, and automated controls into everyday procurement workflows to protect data and strengthen resilience.

What is Cybersecurity Risk in Procurement Software?
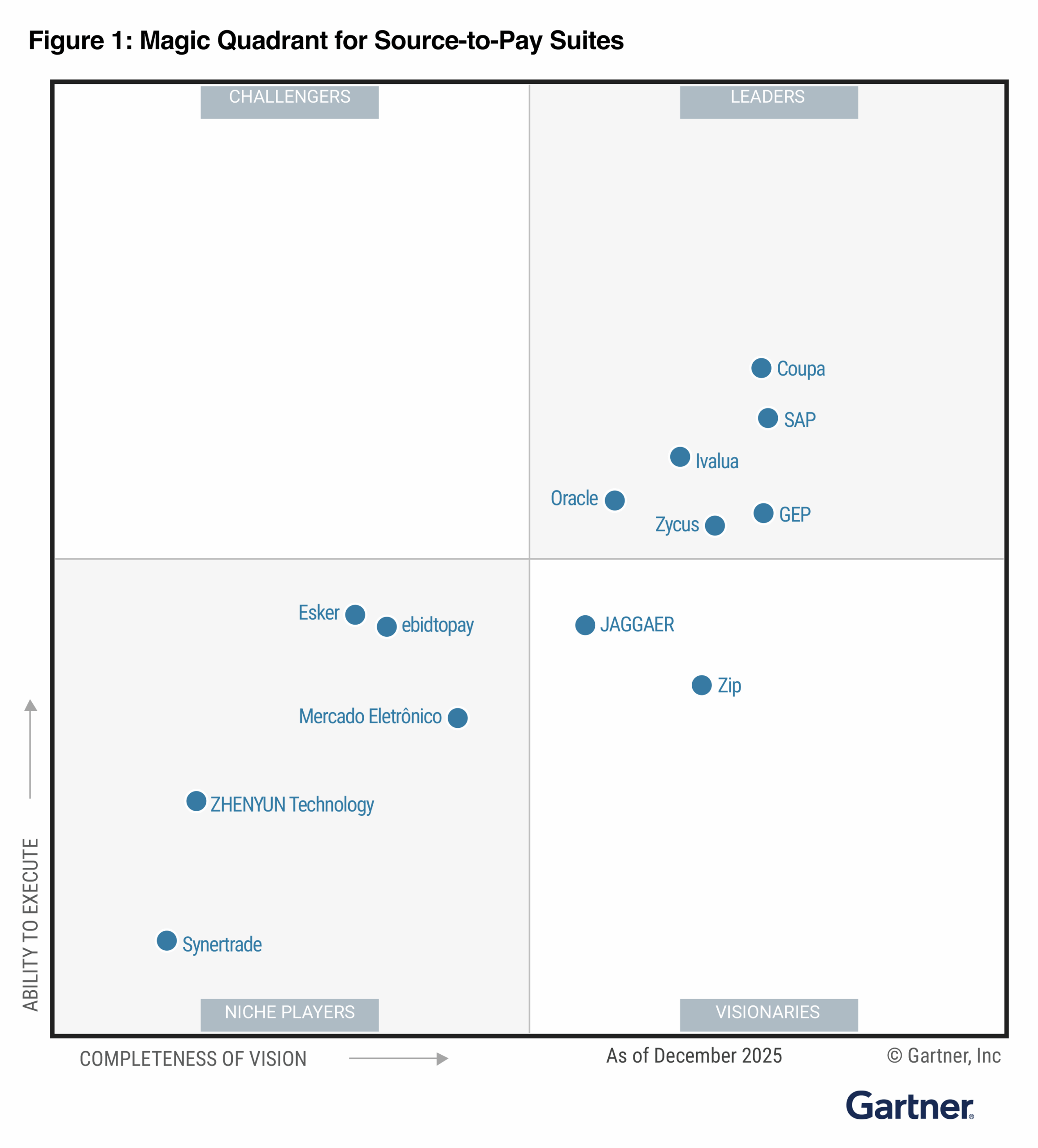
Cybersecurity risk in procurement software is the potential for threats to exploit vulnerabilities across source-to-pay processes and connected systems. Because procurement touches supplier portals, contracts, catalogs, budgets, and payments, controls must be embedded at each step. Zycus unifies these controls within its Source-to-Pay platform, so policy and evidence collection occur automatically during day-to-day work.
Typical exposures include misconfigured permissions, unsecured integrations, shadow data in attachments, and supplier-side compromises. Zycus helps address these with privacy-aware intake, governed catalogs, and automated routing aligned to risk. Explore Zycus eProcurement capabilities for secure buying here and catalog governance here.
Supplier cyber posture also matters. Zycus Supplier Risk Management continuously surfaces signals and ties them to workflows, enabling proactive action. Learn more about supplier risk here and orchestration for compliance and risk here.
- Data protection and privacy-aware intake
- Identity and access management with RBAC and SoD
- Third-party and supplier cyber risk management
- Secure integrations and cloud architecture
- Monitoring, incident response, and audit automation
Why Cybersecurity in Procurement Software Matters
Procurement sits at the crossroads of internal stakeholders and thousands of suppliers, making it a prime target for fraud and data leakage. Zycus orchestration enforces policy at intake and approvals to reduce exposure learn more.
Cloud delivery and extensive connectivity increase the attack surface. Zycus applies governed catalogs, budget controls, and secure integrations to minimize risk while maintaining speed see eProcurement.
Continuous supplier monitoring helps organizations respond to external threats quickly. Zycus surfaces risk signals in-context to pause POs, trigger reviews, or route to alternates.
Audit readiness improves with immutable logs and automated evidence tied to workflows, reducing preparation time and strengthening compliance posture.
How Modern Cybersecurity in Procurement Works
Data Protection and Privacy-Aware Intake
Zycus classifies sensitive fields at the point of capture, minimizes data collection, and enforces encryption and export controls across contracts, invoices, and supplier records. Catalog and document repositories apply granular access and watermarking to discourage misuse. Explore data privacy in intake here and catalog governance here.
Budget and price data benefit from least-privilege views, while governed exports and retention policies reduce exposure learn more.
Identity, Approvals, and Orchestration
Zycus enables SSO, MFA, RBAC, and segregation of duties with dynamic approvals based on value, category, budget, and supplier risk. Procurement orchestration embeds rules at intake and routes exceptions automatically, accelerating compliant buying while maintaining control see orchestration and eProcurement.
Supplier Risk and Continuous Monitoring
Zycus Supplier Risk Management delivers risk-tiered onboarding, continuous signals, in-workflow enforcement, and remediation tracking. When risk rises, the system can auto-pause POs, trigger security reviews, or switch to alternates—keeping operations safe and resilient learn more and performance & risk.
- Privacy-aware intake with controlled exports
- RBAC, SoD, and step-up authentication for high-risk actions
- Risk-tiered supplier onboarding with continuous signals
- Hardened integrations with governed APIs and secrets
- Immutable logs, SIEM-friendly events, and audit-ready evidence
When to Apply Cybersecurity in Procurement
Organizations in regulated and data-sensitive industries benefit from orchestrated, risk-aware procurement. Explore industry approaches for financial services here and healthcare & life sciences here.
- Supplier onboarding for vendors handling PII or financial data
- Catalog and contract repository access for distributed teams
- High-value purchasing with dynamic approvals and budget checks
- Invoice processing and bank detail change governance
- Integrations with ERP, HR, tax, and external content sources
- Continuous monitoring and remediation for critical suppliers
FAQs
−
+
+
+
+
+
+
+
Proof & Case Study
Challenge: A global manufacturer operated decentralized procurement across regions, with email-driven intake, ad-hoc supplier vetting, and inconsistent approvals. Sensitive documents lived in shared drives, supplier bank changes lacked maker-checker controls, and integrations used long-lived credentials. Audit preparation took weeks and fraud attempts increased as volumes grew.
Solution: The company deployed Zycus orchestration with privacy-aware intake, governed catalogs, and dynamic approvals tied to value, category, and budget. Supplier Risk Management added risk-tiered onboarding and continuous signals to auto-pause high-risk orders. eProcurement enforced RBAC/SoD, step-up MFA for bank edits, and controlled exports. API scopes and managed secrets hardened ERP integrations. Immutable logs and automated evidence connected every control to its workflow.
Results: 62% faster cycle time for in-policy requests; 47% reduction in high-risk incidents across supplier master and invoice workflows; 98% evidence completeness at audit with preparation cut from 15 days to 2 days; 35% increase in spend through governed catalogs; and zero successful payment-fraud events in the first two quarters post go-live.
Resources
Explore additional materials to help you implement and optimize your procurement security processes.
Supplier Risk and Performance Management Software | Zycus
Discover multi-dimensional risk and performance management with signals, scorecards, and remediation workflows embedded in procurement.
Supplier Risk Management Software | Zycus
Learn how continuous monitoring, risk-tiered onboarding, and in-workflow enforcement reduce third-party cyber exposure.
Procurement Orchestration for Compliance & Risk Management
See how policy is translated into automated checks at intake and approvals to improve compliance and accelerate safe purchasing.
Zycus eProcurement Software 2025
Explore guided buying, budget controls, and governed catalogs that streamline compliant purchasing across your enterprise.
Procurement Catalog Management Software 2025
Govern your catalogs with role-based access, versioning, and approvals to prevent unauthorized price or content changes.
Procurement Budget Management Software 2025
Align purchasing with budgets and approvals using real-time visibility and controls embedded in buying workflows.
How AI Enhances Data Privacy in Procurement Intake Systems
Understand how AI-driven intake minimizes sensitive data collection and strengthens privacy from the first touchpoint.
Fine Tuning the Procurement Symphony – Part 3: Data Security, Compliance & more
Best practices for embedding data security and compliance throughout the Source-to-Pay lifecycle.
Ready to transform your procurement security?
See how Zycus’ solutions can redefine your procurement and financial operations.